Connected Vehicles and Privacy
I have read a lot of stuff lately about the so-called dangers of connected cars and the inevitability that my car is going to kidnap me and drive me to a dark place and dump me. I'll be lucky to survive, apparently.
That's okay; I'm from Hamilton. I've been driven to dark places and dumped before. Usually I've deserved it.
More aptly, though, I have read a lot more stuff on the perception that connected vehicles (or autonomous vehicles, as they are sometimes called) are inherently dangerous to the preservation of privacy.
Because of the evidence that connected cars are going to reduce accidents, or at least the cost of accidents, significantly, the connected car is not going to go away. (See the McKinsey report, which says that the cost of accidents could go down by as much as 90 percent. Wow.)
There is a terrific (and also terrifying) document called "The Connected Car: Who is in the Driver's Seat?" subtitled, "A study on privacy and onboard vehicle telematics technology". This document was prepared primarily by the very able Philippa Lawson and was published by the British Columbia Freedom of Information and Privacy Association.
Neither of these documents is light reading, but they certainly raise interesting and important issues about the inevitability of connected cars and the need to understand the privacy and data protection implications of them.
It is excellent publications like these, mirrored inadequately in all other media, that spawn in The Great Unwashed (a group in which I include myself, except on Saturday nights, which is bath night) an unquestioning belief that our cars will ultimately betray us, and there's nothing to be done about it.
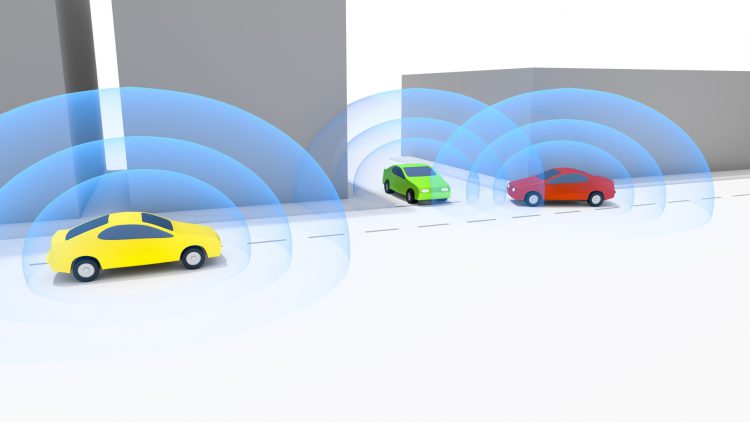
At this point I need to talk a bit about the DSRC (Dedicated Short Range Communications) technology that is at the root of the connected car.
Presciently, in 1999, the U.S. Federal Communications Commission allocated wireless spectrum for "Intelligent Transportation Systems." A few years later, the European Telecommunications Standards Institute followed suit. So the technology that enables connected vehicles is not new. Just for fun, take a look at the United States Department of Transportation Intelligent Transportation Systems Joint Program Office website, where there are some excellent bits of information about DSRC and how it works. It's pretty impressive.
You might also want to take a look at its fact sheet, which takes the 3,048 meter view of DSRC and states that DSRC provides safety message authentication and privacy.
Basically, DSRC devices are natively IPv6 operable. (Your home or work computer is IPv4.) IPv6 makes it easy to inter-connect DSRC devices, like vehicles or roadside infrastructure, to other networks. IPv6 is at the heart of the IEEE 1609 (Wireless Access in Vehicular Environments) suite of specifications pertaining to DSRC.
There are all kinds of uninformed or self-interested allegations that DSRC is bad. These allegations include:
No one has yet mentioned that Chicken Little was right, but I'm sure that someone will get around to that as the hysteria inevitably rises to a fever pitch.
The actual facts differ from the hyperbole, as usual.
The Collision Avoidance Metrics Partnership (CAMP) and the Vehicle Safety Communications (VSC) consortium (which includes several major automakers and the U.S. National Highway Traffic Safety Administration) have paid very close attention to these issues over the past decade, to ensure that DSRC works in a secure and safe manner, and preserves privacy. Privacy is protected through the Security Credentials and Management System (SCMS), the IEEE 1609.2 security specification and the Elliptic Curve Digital Signature Algorithm (ECDSA), among others. [Note: These acronyms are designed to make this blog article look more authentic and knowledgeable. How am I doing?]
Privacy and safety are at the very heart of all these efforts. The published initial requirements specifications in 2011 and the draft specification for SCMS implementation published earlier this year by the USDOT2345 are all about safety and privacy in the connected vehicle.
The result of all these efforts is a connected car system architecture that enables a potentially large-scale deployment of vehicular wireless networking characterized by "Privacy By Design" principles.
While it is true that there have been some well publicized "vehicle hacks" that are fun to read about, the DSRC technology has not been hacked and has nothing to do with the hacks that have taken place to date. The hacks we've all read about arise from the negligent manner in which access to the Controller Area Network bus (CAN bus) was enabled by the inter-networking and protocol architectures sponsored by the cellular industry, which seeks to get into the wireless automotive services business. I know how often my cell phone doesn't work; no way I'm letting those guys control my car.
In fact, LTE based cellular technology, even if made hack-proof, exhibits far too much latency to be useful for a connected car, where a hundredth of a second can make a difference.
On the other hand, it has been demonstrated over and over that interfacing to the CAN bus so that SAE J2735 safety messages can be sent to a connected vehicle does not create a vulnerable cyber-attack means for Internet communications with the outside world. Even if a "rogue" vehicle were somehow created through industrial sabotage at the factory level, the SCMS system would quickly "quarantine" that vehicle because it would lack the IEEE 1609.2 security credentials needed to function. Such a non-compliant vehicle - or it could be any device interfacing with a vehicle or the infrastructure that supports vehicle-to-vehicle (V2V) technology) - would be quickly identified by other nodes in the network and denied access to services and communication.
That's all part of the specification; that's why it works.
I don't mean to imply that anyone who is worried about privacy in the Internet of Things - and most particularly about privacy in connected vehicles - is living on the lunatic fringe. Far from it. I pay attention to privacy too. I'm just saying that if you dig into the actual facts about connected cars and take a hard look at the DSRC technology, you'll discover that you don't have to worry as much as you thought. In fact, you're far more likely to stay alive, and private, in a connected car than you are today in a conventional car driven by some guy who is probably texting his buddies to meet them for a few brewskies after work.
Just saying.

